The global landscape of digital innovation is undergoing a profound transformation, marked by divergent paths in the evolution of two foundational technologies: Bitcoin and artificial intelligence. While Bitcoin mining operations are increasingly consolidating and migrating to regions offering cost-effective energy, AI development appears poised for a more decentralized future, driven by advancements in edge computing. This contrasting trajectory highlights the complex interplay of economic incentives, technological advancements, and the enduring quest for resilience in digital infrastructure.
Recent analyses indicate a significant shift in Bitcoin mining operations, with costs in some parts of the United States surpassing $100,000 for a single Bitcoin. This escalating operational burden is compelling numerous operators to relocate, seeking more economically viable environments. Among the most prominent emerging destinations are Paraguay and Ethiopia, both countries distinguished by their abundant surplus hydroelectric power, which translates into substantially lower electricity bills – a critical factor for the energy-intensive process of cryptocurrency mining.
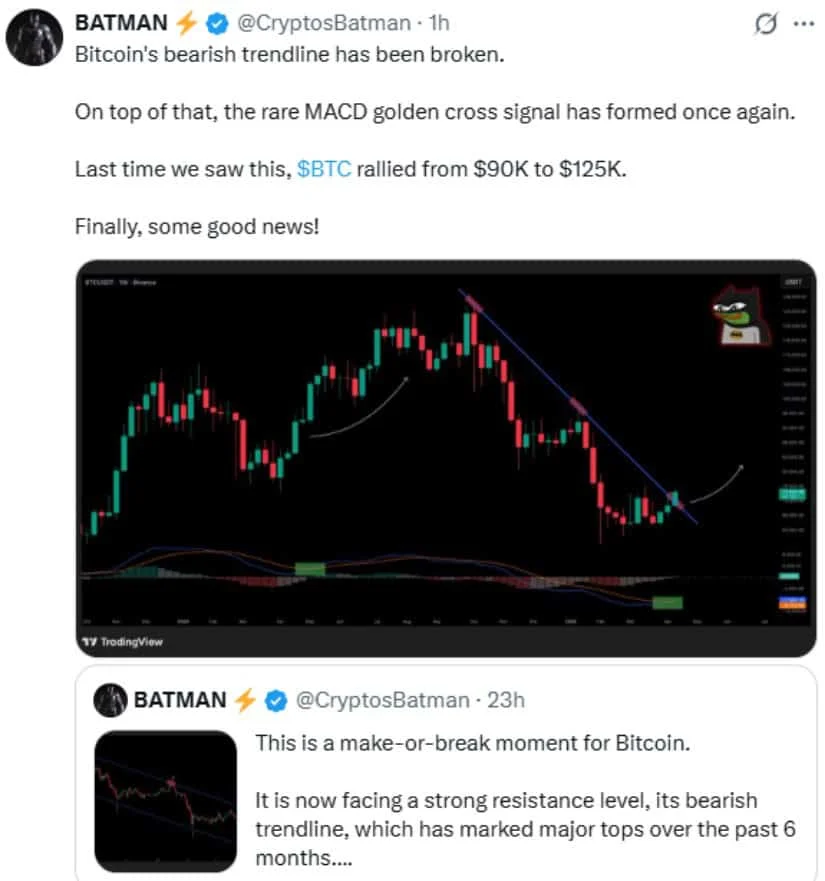
According to insights from crypto exchange KuCoin, this geographical redistribution of mining activity is already well underway, with a discernible migration of the Bitcoin network’s hash rate towards what analysts have termed the "Global South." This movement is not merely an economic rebalancing but, as KuCoin argues, a strategic strengthening of the Bitcoin network. By diversifying its geographical footprint, the network inherently reduces its vulnerability to political instability, regulatory pressures, or energy supply shocks originating from any single nation or region. This represents a distinct form of decentralization – perhaps not the immediate vision of a network run on individual computers as envisioned by Satoshi Nakamoto, but a vital decentralization of physical infrastructure and political risk nonetheless.
The Economic Imperative: Why Bitcoin Mining is Moving
The decision to relocate a Bitcoin mining operation is driven primarily by an acute economic reality: profitability. Bitcoin mining is a highly competitive industry where margins can be razor-thin, heavily influenced by two main factors: the price of Bitcoin and the cost of electricity. As the network’s difficulty adjusts and halving events reduce block rewards (e.g., the recent April 2024 halving that cut rewards from 6.25 BTC to 3.125 BTC per block), the efficiency of mining hardware (ASICs) and the cost of power become paramount.
In the United States, while certain states like Texas and Kentucky initially attracted miners post-China’s 2021 ban due to deregulated energy markets and supportive policies, the energy landscape has become more challenging. Increased demand, infrastructure limitations, and sometimes volatile energy prices have pushed operational costs upwards. Reports citing mining costs exceeding $100,000 per Bitcoin suggest that for many miners, operating within these regions becomes unsustainable, especially when Bitcoin’s market price hovers below or around that threshold. For instance, with Bitcoin trading around $70,000, a $100,000 mining cost signifies a substantial loss per coin. This stark economic calculus leaves operators with little choice but to seek more favorable conditions.
The migration towards the Global South, particularly to nations like Paraguay and Ethiopia, is a testament to the pursuit of cheap, reliable, and often renewable energy sources. Paraguay, for example, boasts the Itaipu Dam, one of the world’s largest hydroelectric power plants, which generates significantly more electricity than the country consumes. This surplus energy is not only abundant but also comes at a fraction of the cost found in many developed nations. Similarly, Ethiopia is investing heavily in hydroelectric projects, such as the Grand Ethiopian Renaissance Dam (GERD), positioning itself with considerable energy reserves. These regions offer a unique combination of low energy costs, often supported by government incentives to attract foreign investment, and a relatively stable regulatory environment that views Bitcoin mining as a potential economic boon.
The chronology of Bitcoin mining has seen several significant shifts. It began with hobbyists using CPUs in 2009, moving to GPUs for increased efficiency, and then fundamentally transforming with the introduction of Application-Specific Integrated Circuits (ASICs) in the early 2010s. ASICs, designed solely for Bitcoin mining, vastly outcompeted general-purpose hardware, ushering in an era of industrial-scale mining farms. The 2021 crackdown on Bitcoin mining in China, which had historically dominated the hash rate, led to a massive exodus of miners to other regions, including the United States, Kazakhstan, and Canada. This latest shift to the Global South represents another phase in the ongoing global reallocation of hash power, driven by an ever-present search for efficiency and lower costs.
From a broader perspective, this geographic decentralization enhances the Bitcoin network’s robustness. A network where hash power is distributed across multiple political jurisdictions is inherently more resistant to potential coordinated state-level attacks or regulatory overreach aimed at disrupting the network. While the concentration of hardware into large industrial facilities might appear to centralize mining power within a few hands, the global dispersion mitigates the risk associated with any single nation gaining undue influence over the network’s operation.
The Opposite Paths: Bitcoin’s Centralization vs. AI’s Decentralization
In stark contrast to Bitcoin’s evolving path towards geographically dispersed but industrially concentrated mining, the field of artificial intelligence appears to be embarking on a journey towards greater decentralization, particularly through the paradigm of edge computing. This insightful observation was articulated by Alex Thorn, head of research at Galaxy, who highlighted the inverse trajectories of these two transformative technologies.
Thorn noted that Bitcoin mining began in a highly decentralized manner, with individual participants utilizing standard CPUs and later GPUs on their home computers. Over time, the relentless pursuit of efficiency led to the dominance of specialized ASIC hardware and the establishment of massive, industrial-scale mining farms. This evolution effectively centralized mining power into the hands of a few large entities capable of investing in vast arrays of specialized hardware and securing access to cheap energy. The gap between a casual participant and a serious miner has widened to an unbridgeable chasm.

Conversely, artificial intelligence started its life deeply centralized, primarily within the confines of massive, corporate-controlled data centers. The development and training of frontier AI models – the cutting-edge large language models and advanced neural networks – require immense computational resources, vast datasets, and specialized infrastructure, traditionally housed by tech giants. These models are typically accessed remotely through cloud services, with data being sent to central servers for processing.
However, a significant shift is now underway. As frontier models encounter inherent constraints – including data scarcity for further training, limitations in context windows, and memory bottlenecks – open-source alternatives and smaller, more efficient models are rapidly gaining traction. These more compact AI models are becoming increasingly capable and, crucially, cheaper to run. A growing number of them can now operate directly on personal devices such as smartphones and laptops, bypassing the need for constant communication with remote data centers.
As Thorn succinctly put it, "If local models keep getting smaller, cheaper, and more efficient, AI may become increasingly personal and on-device." This shift empowers individual users and smaller enterprises with advanced AI capabilities without relying exclusively on centralized infrastructure.
The Rise of Edge AI: A $119 Billion Market Taking Shape
This push towards on-device AI processing is formally known as edge computing. It refers to the practice of performing computations and running AI models locally, on the "edge" of the network – meaning on the device itself or a local gateway – rather than routing all data to a distant cloud server for processing. This paradigm offers numerous advantages that are fueling its rapid adoption and market expansion.
According to market research, the global edge AI market was valued at approximately $25 billion in 2025. Projections from Grand View Research estimate this figure to surge to nearly $120 billion by 2033, representing an astonishing growth of almost 300% over an eight-year period. This exponential growth is underpinned by several powerful trends:
- Proliferation of Connected Devices: The explosion of IoT devices, from smart home appliances to industrial sensors and autonomous vehicles, creates an unprecedented volume of data at the network edge.
- Demand for Real-Time Processing: Many critical applications, particularly in sectors like manufacturing, healthcare, and autonomous systems, cannot tolerate the latency introduced by sending data to the cloud and waiting for a response. Edge AI enables instantaneous decision-making. For instance, an autonomous vehicle needs to process sensor data in milliseconds to avoid a collision, a task unsuited for cloud-based AI.
- Growing Concern Over Data Privacy and Security: Processing sensitive data locally on a device reduces the risk of data breaches associated with transmitting and storing information on centralized cloud servers. This is particularly crucial for industries handling personal health information (PHI) or proprietary industrial data.
- Reduced Bandwidth and Cloud Costs: By performing computations locally, the amount of data that needs to be sent to the cloud is significantly reduced, leading to lower bandwidth consumption and decreased operational costs for cloud services.
Industries that inherently demand minimal delays are at the forefront of driving edge AI adoption. In manufacturing, edge AI can power predictive maintenance, quality control, and robotic automation directly on the factory floor. In healthcare, it enables real-time diagnostics on medical devices, remote patient monitoring, and personalized health insights without sensitive data leaving the local environment. Logistics companies utilize edge AI for optimizing routes, managing inventory, and enhancing last-mile delivery efficiency. The integration of 5G networks further accelerates this trend, providing the high-speed, low-latency connectivity essential for effective edge deployments.
Broader Implications and the Future Landscape
The contrasting trajectories of Bitcoin mining and AI decentralization carry significant implications for technology, economics, and society.
For Bitcoin, the increasing concentration of mining power, even if geographically diversified, continues to raise questions about long-term network security and the core ethos of decentralization. A network where a relatively small number of large players control a substantial portion of the hash rate is, theoretically, more susceptible to disruption, such as a 51% attack, than one distributed across thousands of truly independent operators. While the migration away from the US towards the Global South may mitigate some of the geopolitical risks, the fundamental industrial consolidation remains a point of ongoing debate within the Bitcoin community. The environmental footprint of mining also remains a concern, though the shift towards hydroelectric power in new hubs offers a more sustainable energy mix. Host countries in the Global South stand to benefit from inward investment, job creation, and the utilization of surplus energy, potentially fostering new economic sectors.
For AI, the move towards decentralization through edge computing offers a more democratic and accessible future. By enabling AI models to run on everyday devices, it lowers the barrier to entry for developers and users, fostering innovation and personalized experiences. This paradigm shift could accelerate the development of specialized AI applications, enhance privacy for individuals, and create new business models centered on localized intelligence. However, it also introduces challenges related to managing and securing a vast, distributed network of AI-powered devices, as well as ensuring the ethical deployment of AI across a multitude of local contexts.
Ultimately, the stories of Bitcoin and AI, though moving in different directions concerning their operational decentralization, both underscore the dynamic nature of technological evolution. They reflect the continuous adaptation to economic pressures, the relentless pursuit of efficiency, and the foundational drive to build more robust, resilient, and impactful digital systems. The coming years will undoubtedly reveal how these divergent paths shape the global digital economy and influence the very fabric of our increasingly connected world.