The rapid evolution of the Web3 ecosystem has introduced a paradigm shift in how individuals interact with digital value, moving away from centralized financial institutions toward a model of absolute self-sovereignty. However, this transition to a decentralized landscape brings with it a critical caveat: the burden of security rests entirely on the end user. In the world of blockchain, there are no "undo" buttons, no customer service hotlines to reverse a fraudulent transaction, and no centralized authorities to recover lost private keys. As the adoption of non-fungible tokens (NFTs), decentralized finance (DeFi), and blockchain-based gaming continues to accelerate, understanding the nuances of digital asset protection has become a fundamental requirement for any participant in the digital economy.
The Foundation of Web3: The Reality of Self-Responsibility
At its core, Web3 is built on the principle of decentralization, which removes intermediaries like banks or tech conglomerates. In traditional Web2 environments, a forgotten password can be reset via email, and a fraudulent credit card charge can be disputed through a bank. In Web3, users employ non-custodial wallets, such as MetaMask or Trust Wallet, where they alone hold the private keys or "seed phrases" that grant access to their assets.
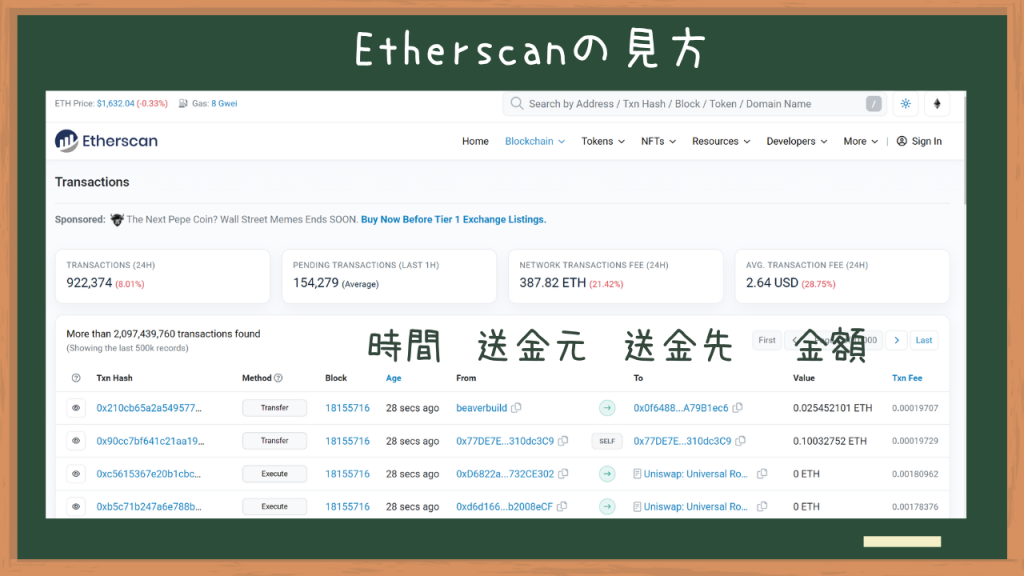
The transparency of the blockchain, while a cornerstone of its integrity, also presents unique risks. Every transaction, balance, and asset movement is recorded on a public ledger. Platforms such as Etherscan (for the Ethereum network) or BSCScan (for the BNB Smart Chain) allow anyone to input a wallet address and view its entire history. For malicious actors, this transparency serves as a roadmap. Scammers can monitor high-value wallets—often referred to as "whales"—or track users participating in specific "trending" projects to tailor their social engineering attacks. When a user interacts with a decentralized application (dApp), they are essentially interacting with smart contracts, and any lapse in judgment can lead to the immediate and irreversible draining of their digital holdings.

Chronology of the Scam Evolution: From Simple Phishing to Sophisticated Drainers
The methods used by cybercriminals in the Web3 space have evolved significantly since the early days of Bitcoin. Initially, scams were limited to simple "giveaway" frauds where users were asked to send crypto to an address with the promise of receiving double in return. Today, the tactics are far more insidious and technically complex.
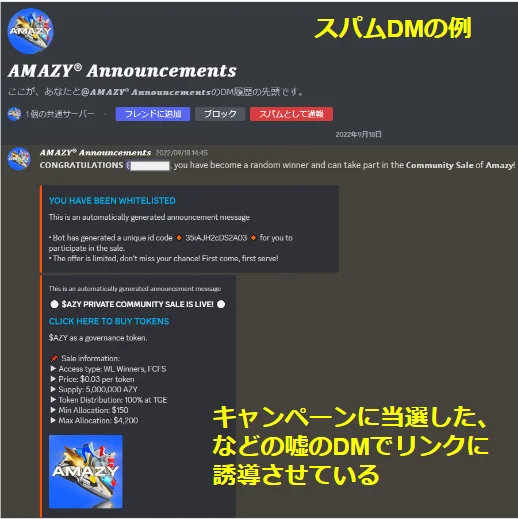
- Social Engineering and Community Compromise (2021–Present): As Discord and X (formerly Twitter) became the primary hubs for Web3 communities, scammers began targeting these platforms. By compromising the accounts of project founders or Discord moderators, attackers post "emergency" or "stealth mint" links. Users, driven by the "Fear Of Missing Out" (FOMO), often click these links and connect their wallets without performing due diligence.
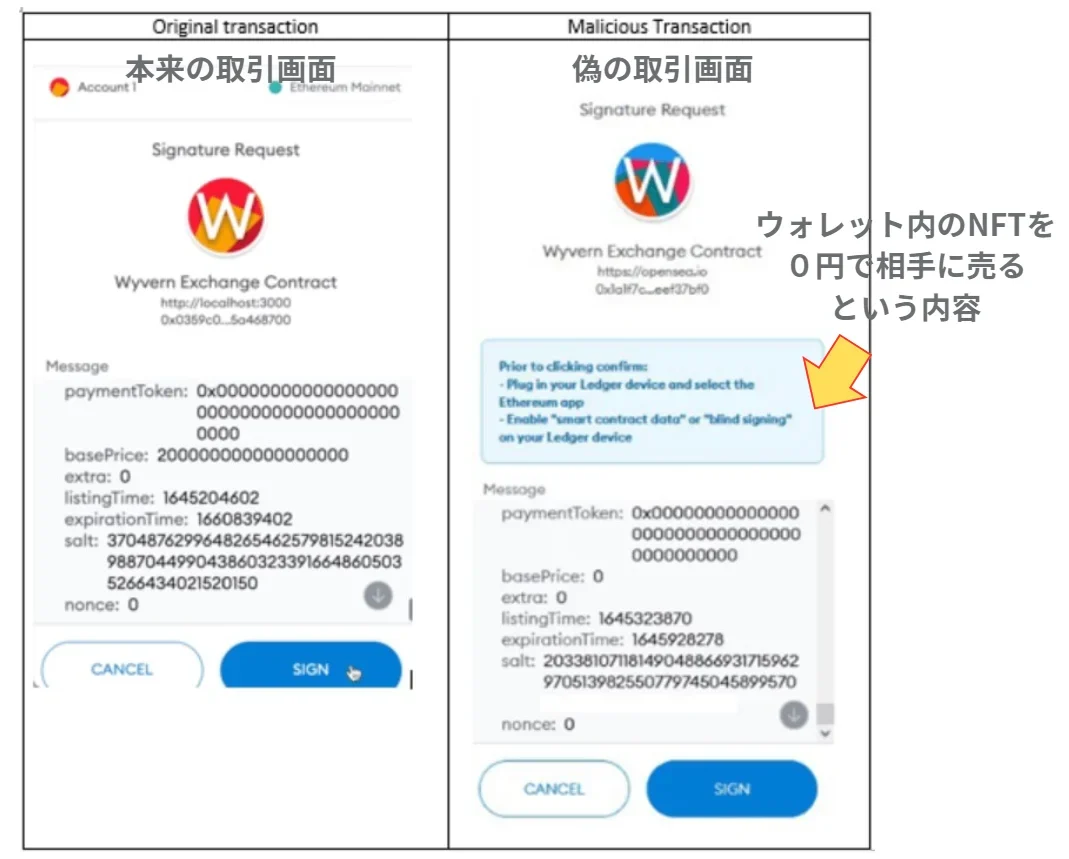
- The Rise of Phishing Clones (2022–Present): Attackers create pixel-perfect replicas of popular marketplaces like OpenSea or Uniswap. These sites are often promoted through paid Google search ads, appearing at the top of search results. When a user attempts to "login" or "connect," they are prompted to sign a transaction that grants the attacker full permission to transfer their assets.
- Wallet Drainers and Malicious Signatures: The most recent evolution involves "drainer" scripts. These are sophisticated pieces of code that, once a wallet is connected to a site, scan the wallet for its most valuable assets (ETH, Bored Ape NFTs, stablecoins) and present a series of signature requests. To the untrained eye, these look like standard login prompts, but they are actually "SetApprovalForAll" or "Permit" functions that authorize the attacker to withdraw everything.
Supporting Data: The Economic Impact of Web3 Vulnerabilities
The scale of the threat is underscored by recent industry data. According to reports from blockchain security firms such as Immunefi and Chainalysis, the total value lost to hacks and scams in the crypto space has consistently reached billions of dollars annually. In 2023 alone, it was estimated that over $1.8 billion was lost across the ecosystem. Phishing attacks, specifically those targeting individual wallets through social media, accounted for a significant portion of these losses, particularly in the NFT sector where individual assets can be worth tens of thousands of dollars.

Furthermore, a study of "Rug Pulls"—where developers abandon a project and run away with investors’ funds—reveals that approximately 25% of all new tokens launched in certain periods exhibited characteristics of fraudulent intent. This data highlights the necessity of not only technical security but also rigorous project vetting.
Critical Security Protocols for Digital Asset Protection
To navigate this environment safely, users must adopt a multi-layered security strategy that addresses both technical vulnerabilities and psychological manipulation.

The Danger of Direct Messages (DMs)
On platforms like Discord and X, the default setting for any Web3 participant should be to disable Direct Messages from strangers. Scammers frequently use DMs to send "congratulatory" messages regarding fake airdrops or whitelist spots. Legitimate Web3 projects almost never reach out to individual users via DM to offer prizes. If a message claims you have "won" a contest you did not enter, or requires you to "act now" to claim a reward, it is invariably a phishing attempt.
Verifying Official Links
Users should never rely on search engines or social media posts for access to dApps. Instead, they should use "Linktree" profiles found in the official bios of verified project accounts or bookmark the official URLs once they have been confirmed. Comparing the URL character by character is essential, as "typosquatting" (e.g., using 0pensea.io instead of opensea.io) is a common tactic.

Implementing Security Extensions
A new generation of Web3 security tools has emerged to provide a safety net. Browser extensions like "Kekkai" or "Pocket Universe" act as a firewall for your wallet. When a user is asked to sign a transaction, these tools simulate the transaction in a sandboxed environment and show the user exactly what will leave their wallet before they sign. If a site is attempting to drain an NFT, the extension will display a prominent warning, potentially saving the user from a catastrophic loss.
The "Revoke" Mechanism: Managing Smart Contract Permissions
One of the most misunderstood aspects of Web3 security is the concept of "Token Approvals." When you trade on a platform like Uniswap or list an NFT on OpenSea, you must grant that platform’s smart contract permission to move your tokens. However, if a user accidentally grants this permission to a malicious site, the attacker can drain the wallet even days or weeks later.
How to Revoke Permissions
To mitigate this risk, users must regularly audit and "revoke" their approvals. This process essentially tells the blockchain to cancel the permission previously granted to a specific contract.
- Access a Scan Tool: Navigate to the "Token Approval" section of a block explorer. For Ethereum, this is found at
etherscan.io/tokenapprovalchecker. For BNB Chain, it isbscscan.com/tokenapprovalchecker. - Connect Web3 Wallet: Click the "Connect to Web3" button to link your wallet to the explorer. This allows the tool to read your current active approvals.
- Audit the List: The tool will display a list of all contracts that have permission to spend your tokens or move your NFTs.
- Execute the Revoke: For any unfamiliar or suspicious contracts, click the "Revoke" button. This requires a small "gas fee" (transaction fee) because it involves writing a new instruction to the blockchain.
- Confirmation: Once the transaction is confirmed, the contract no longer has access to your assets.
Official Responses and the Move Toward Better UX
The prevalence of these attacks has prompted responses from both wallet providers and regulatory bodies. The developers of MetaMask, for instance, have introduced improved warning labels for "SetApprovalForAll" requests, making it clearer when a user is granting broad permissions. Similarly, the "Seaport" protocol used by OpenSea was designed to make signatures more readable and harder to spoof.

From a regulatory perspective, governments in jurisdictions like the EU (via the MiCA regulation) and the United States are increasingly looking at how to protect consumers without stifling innovation. However, most experts agree that because of the decentralized nature of the technology, regulation can only do so much; the primary defense will always be user education.
Broader Impact and Future Implications
The current state of Web3 security is often cited as the single greatest barrier to mass adoption. For the average person, the fear of losing their life savings due to a single misclick is a significant deterrent. As the industry moves forward, we are likely to see a rise in "Account Abstraction" (ERC-4337). This technology allows for "smart contract wallets" that can have social recovery features, daily spending limits, and two-factor authentication (2FA) directly on the blockchain.
Until these advanced features become the standard, the "self-responsibility" model remains the status quo. The difference between a successful Web3 experience and a devastating loss often comes down to five seconds of hesitation—time used to verify a URL, check a transaction simulation, or double-check a Discord announcement. In the digital frontier, vigilance is the only true insurance.