The transition from the traditional centralized internet to the decentralized framework known as Web3 has introduced unprecedented opportunities for financial autonomy and digital ownership, yet it has simultaneously birthed a sophisticated new era of cyber threats. In the current blockchain ecosystem, the lack of traditional intermediaries—such as banks or centralized customer support—means that the burden of security falls entirely on the individual user. This "self-responsibility" doctrine is the cornerstone of Web3, but it also creates a high-stakes environment where a single mistake can lead to the permanent loss of digital assets, including cryptocurrencies and Non-Fungible Tokens (NFTs). As blockchain gaming and decentralized finance (DeFi) continue to attract a global audience, understanding the mechanics of security, from social engineering tactics to technical mitigation strategies like "revoking" permissions, has become an essential skill for any digital participant.
The Doctrine of Self-Responsibility in a Decentralized World
In a traditional banking system, a fraudulent transaction can often be contested or reversed through a central authority. Web3 operates on a fundamentally different premise: decentralization. While this provides users with total control over their assets, it removes the safety net that most modern consumers have come to expect. Once a transaction is broadcast to the blockchain and confirmed, it is immutable. There is no "undo" button, and there is no governing body to petition for a refund.
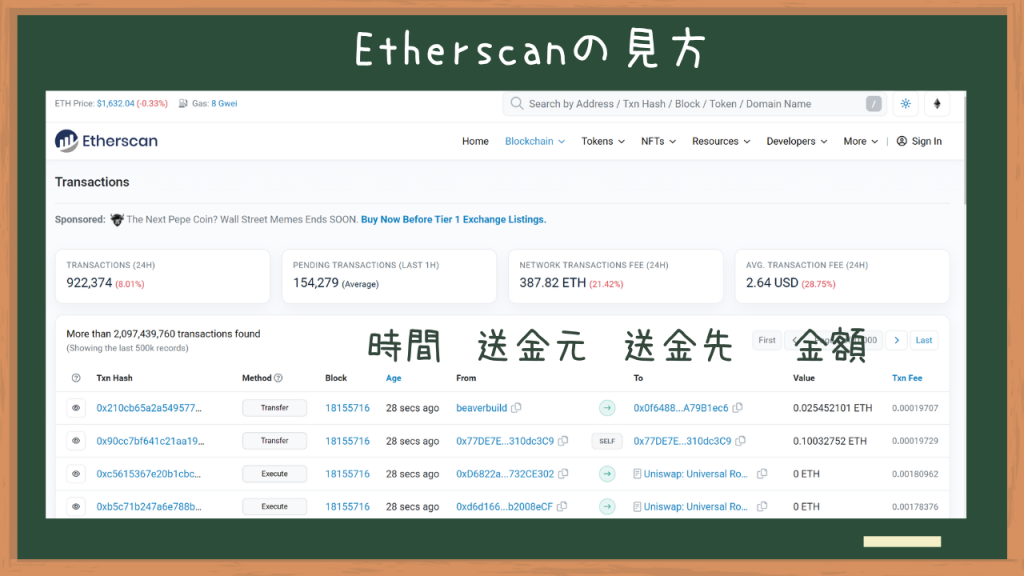
The transparency of the blockchain, while a virtue for auditing and trust, also serves as a roadmap for malicious actors. Tools such as Etherscan and BSCScan allow anyone to input a wallet address and view its entire transaction history, current holdings, and the value of assets stored within. For scammers, these block explorers serve as a lead-generation tool. By identifying "whales"—wallets with high-value holdings—malicious actors can tailor their social engineering attacks with precision, knowing exactly what assets a user possesses and which decentralized applications (dApps) they frequently interact with.

Anatomy of a Web3 Scam: Social Engineering and Phishing
The most prevalent threats in the Web3 space are not technical hacks of the blockchain itself, but rather social engineering attacks that exploit human psychology. These attacks typically manifest through two primary vectors: social media direct messages (DMs) and phishing websites.
The Discord and X (Twitter) DM Trap
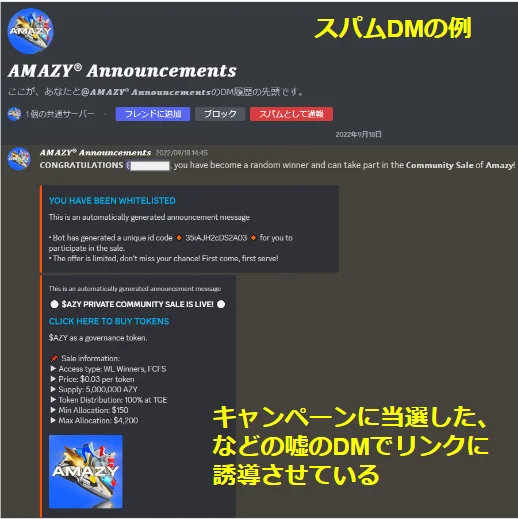
Platforms like Discord and X are the hubs of the Web3 community, but they are also primary hunting grounds for scammers. A common tactic involves sending unsolicited DMs to users participating in specific NFT or gaming communities. These messages often masquerade as "official" notifications from project administrators, claiming the user has won a rare giveaway, been selected for an exclusive "whitelist," or must take urgent action to "save" their assets from a purported hack.

A critical rule of thumb for Web3 participants is that official projects almost never initiate contact via DMs. Most established communities have moved toward a "No DM" policy, explicitly stating that staff will never message users first. Despite these warnings, the allure of a high-value win or the fear of loss remains a powerful motivator for victims to click on malicious links.
The Proliferation of Fake Marketplaces and dApps
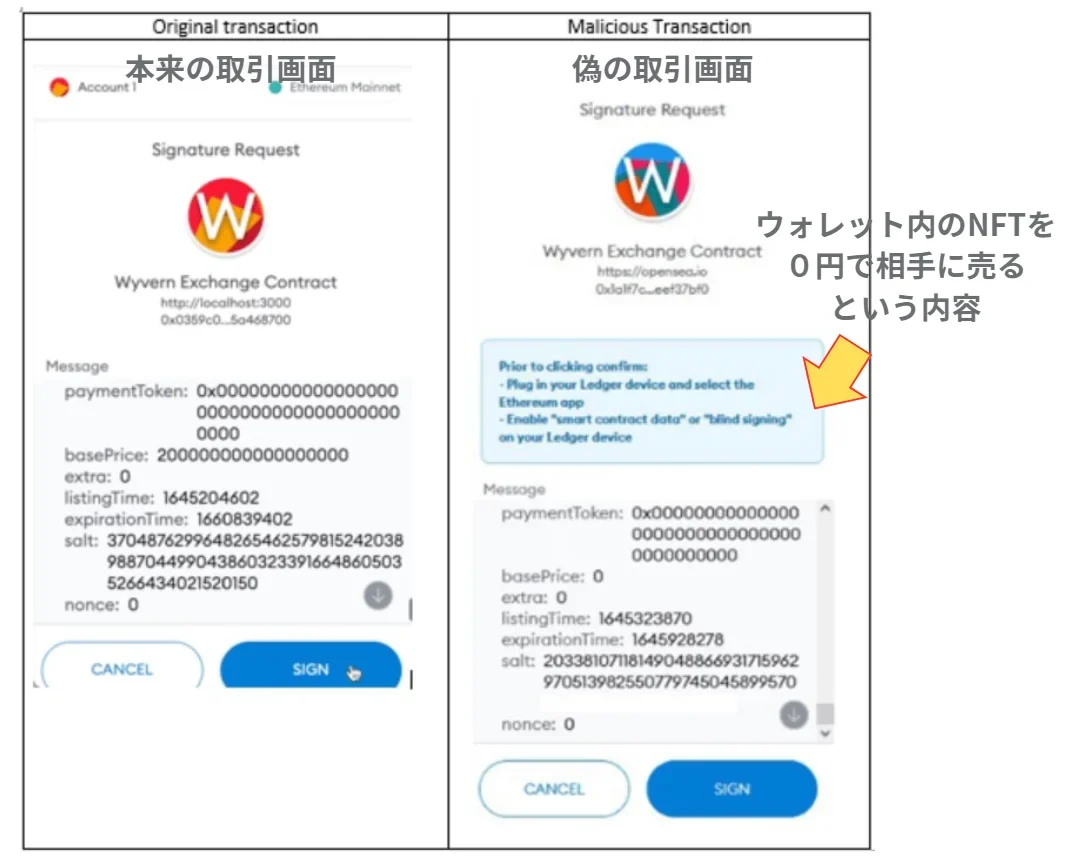
Phishing in Web3 often involves the creation of pixel-perfect clones of popular websites, such as OpenSea or MetaMask. A user might receive a link to what appears to be a legitimate NFT marketplace. Upon arriving at the site, they are prompted to "connect their wallet." Once the connection is established, the site may present a signature request or a transaction approval. If the user signs this request without careful inspection, they may unknowingly grant the malicious site permission to transfer all assets out of their wallet.

Recent data suggests that phishing attacks have become increasingly sophisticated, utilizing "drainer" scripts that can automatically scan a wallet for its most valuable assets and prioritize their theft in a single transaction. These scripts are often sold as "service kits" on the dark web, lowering the barrier to entry for cybercriminals.
Proactive Security Measures: Building a Digital Fortress
To navigate this landscape safely, users must move beyond basic password management and adopt a multi-layered security strategy.

Privacy Settings and Communication Hygiene
The first line of defense is limiting the "attack surface." This involves disabling DMs on platforms like Discord and X. By restricting who can contact them, users can eliminate the vast majority of phishing attempts before they even reach their inbox. Furthermore, users should never share their "seed phrase" or "secret recovery phrase" with anyone. No legitimate service, support team, or developer will ever ask for this information. The seed phrase is the master key to the wallet; anyone who possesses it has total, irreversible control over the funds.
Security Extensions and Real-Time Monitoring
The industry has responded to the rise in phishing by developing specialized security tools. Browser extensions like "Kekkai" (meaning "boundary" or "barrier" in Japanese) act as an intermediary between the user and the dApp. These tools analyze transaction requests in real-time, providing a clear, human-readable summary of what the transaction will do before the user signs it. If a site is known to be malicious or if a transaction involves a suspicious transfer of permissions, the extension will trigger a warning. This added layer of verification is crucial for preventing "approval scams," where users are tricked into giving a contract permission to spend their tokens.
The "Revoke" Mechanism: A Technical Emergency Guide
One of the most misunderstood aspects of Web3 security is the "token approval" system. When a user interacts with a legitimate dApp—such as a decentralized exchange like Uniswap—they must grant the smart contract permission to "spend" their tokens. While this is necessary for the dApp to function, it creates a lingering risk. If that smart contract is later compromised, or if the user accidentally granted permission to a malicious site, their assets remain vulnerable as long as that approval exists.
How to Revoke Permissions
"Revoking" is the process of canceling these permissions. It is a critical hygiene practice that should be performed regularly. The process typically involves the following steps:

- Access a Block Explorer: Navigate to a site like Etherscan (for Ethereum), BSCScan (for BNB Chain), or PolygonScan.
- Locate Token Approvals: Under the "More" menu on Etherscan, users can find the "Token Approvals" tool.
- Connect to Web3: The user must connect their wallet (e.g., MetaMask) to the block explorer to view their active permissions.
- Identify and Revoke: The tool will list every contract that has permission to spend the user’s tokens. Users can then select "Revoke" for any suspicious or unnecessary entries.
- Confirm the Transaction: Revoking is an on-chain action, meaning it requires a small amount of "gas" (transaction fees) to process. Once confirmed, the link between the wallet and the potentially dangerous contract is severed.
Financial Impact and Broader Industry Implications
The financial toll of Web3 security breaches is staggering. According to blockchain analytics firm Chainalysis, crypto-related scams and hacks resulted in the loss of billions of dollars in 2023 alone. While large-scale protocol hacks often make headlines, the cumulative total of individual phishing victims represents a significant portion of total ecosystem losses.
This climate of risk has significant implications for the mass adoption of blockchain technology. For Web3 to reach the "next billion users," the industry must bridge the gap between the current "Wild West" environment and a more user-friendly, secure experience. This includes the development of "Account Abstraction" (ERC-4337), which allows for more complex wallet logic, such as social recovery (recovering a wallet through friends) and transaction limits, mimicking the safety features of traditional banking.
Chronology of Web3 Security Evolution
The history of Web3 security can be categorized into three distinct eras:
- 2009–2017: The Era of Direct Theft. Early attacks were focused on stealing private keys through malware or hacking centralized exchanges (e.g., the Mt. Gox collapse).
- 2018–2021: The DeFi and Smart Contract Boom. As DeFi grew, attackers shifted their focus to exploiting vulnerabilities in the code of smart contracts (e.g., the DAO hack or various flash loan attacks).
- 2022–Present: The Social Engineering Renaissance. With protocol security improving, malicious actors have returned to targeting the "weakest link": the human user. This era is defined by sophisticated phishing, Discord hacks, and the use of "drainer" scripts.
Conclusion: The Future of Digital Safety
As the digital landscape evolves, the definition of security is shifting from a passive state to an active practice. In Web3, safety is not a product one buys, but a set of behaviors one adopts. The integration of better UI/UX, real-time monitoring tools like Kekkai, and a broader public understanding of technical concepts like "revoking" are essential steps in maturing the ecosystem. While the decentralized world offers unparalleled freedom, that freedom is inextricably linked to the vigilance of the individual. By staying informed, practicing strict communication hygiene, and utilizing the technical tools at their disposal, users can protect their digital legacy in the burgeoning world of Web3.