The rapid expansion of the decentralized finance (DeFi) and non-fungible token (NFT) ecosystems has introduced a new paradigm of asset ownership, but it has also birthed sophisticated methods of digital asset theft. Among the most prevalent vulnerabilities is the misuse of the "Approve" function within smart contracts. While this function is essential for the operation of decentralized applications (DApps), it has become a primary vector for phishing attacks and contract exploits. Security analysts and blockchain forensics firms have increasingly warned that the practice of granting "infinite approvals" to various platforms, combined with the proliferation of phishing sites, has led to billions of dollars in losses. To safeguard assets, users must understand the fundamental mechanics of smart contract permissions and the critical necessity of the "Revoke" function.

The Mechanics of the Approve Function in Blockchain Transactions
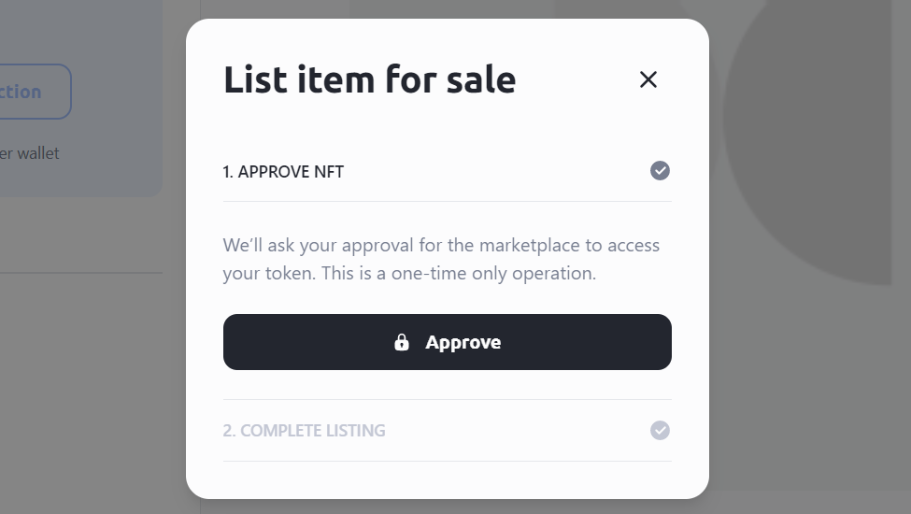
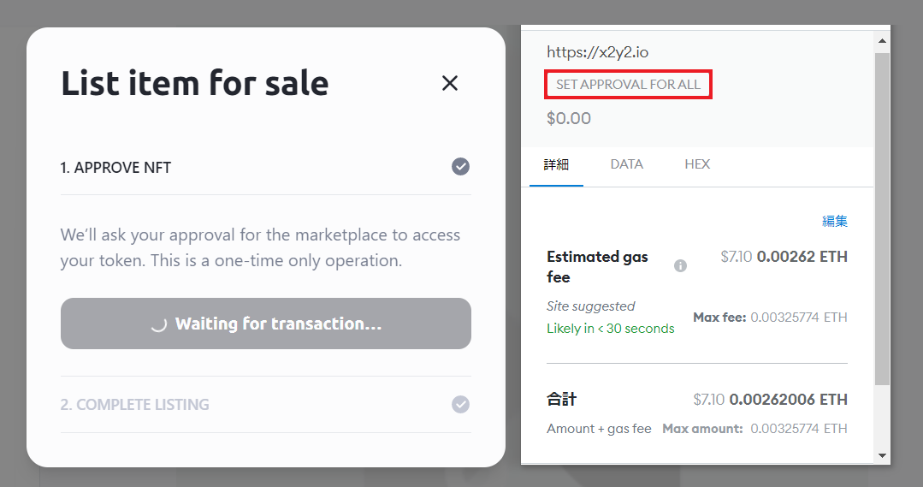
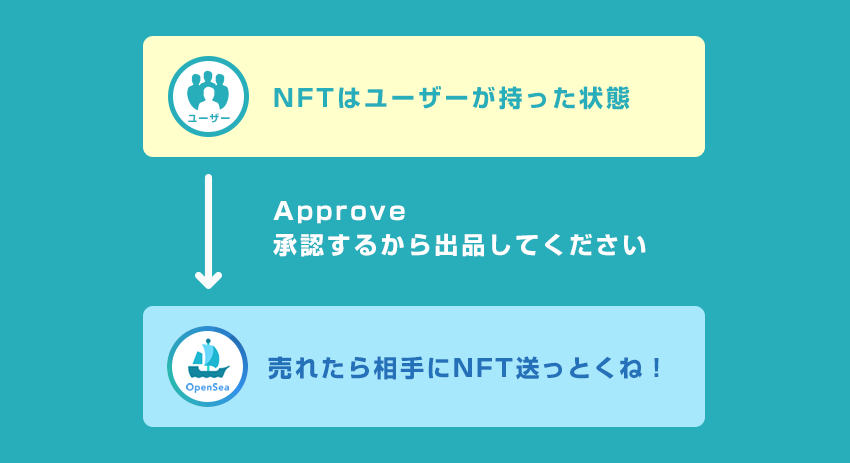
At its core, the "Approve" function is a standard feature of ERC-20 (tokens) and ERC-721/ERC-1155 (NFTs) smart contracts on Ethereum and compatible networks. Because a decentralized exchange (DEX) like Uniswap or an NFT marketplace like OpenSea does not have custody of a user’s private keys, it cannot move assets on the user’s behalf without explicit permission. The "Approve" transaction serves as this permission. When a user wishes to list an NFT for sale or swap one token for another, they must first sign an approval transaction that authorizes the marketplace’s smart contract to transfer the specific asset once a buyer is found or a trade is executed.
However, for the sake of user convenience and to minimize gas fees, many DApps request "Infinite Approval." This grants the contract the right to move an unlimited amount of a specific token from the user’s wallet at any time in the future. While this prevents the user from having to sign—and pay for—an approval transaction every time they trade, it creates a persistent "open door" to the wallet. If that smart contract is later compromised, or if the user accidentally grants this permission to a malicious contract disguised as a legitimate service, the attacker can drain the wallet’s contents without further interaction from the owner.

The Anatomy of an Approval-Based Phishing Attack
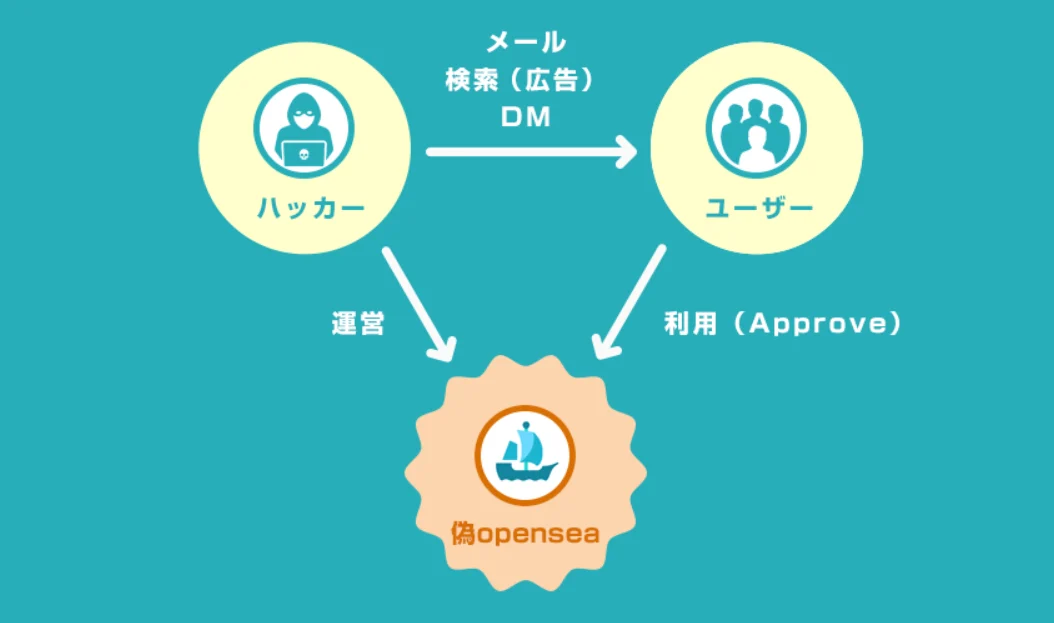
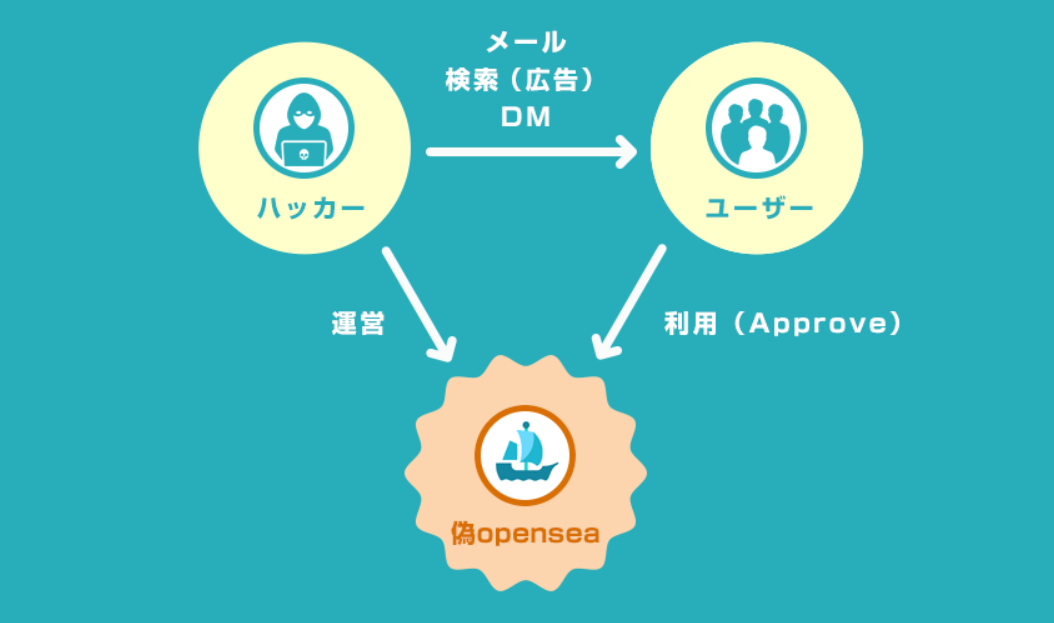
The most common method of exploiting this mechanism is through phishing. Malicious actors create high-fidelity replicas of popular platforms such as OpenSea, Blur, or MetaMask. These fraudulent sites are often promoted through compromised Discord bots, "sponsored" search results on major search engines, or direct messages on social media.
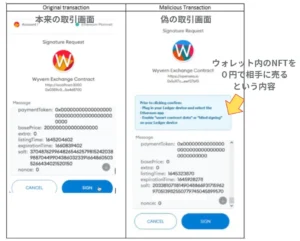
When a victim connects their wallet to a phishing site, they are prompted to sign a transaction that appears to be a routine login or a "free mint" opportunity. In reality, the transaction is a "SetApprovalForAll" request. This specific command is particularly dangerous for NFT collectors, as it grants the attacker’s contract the power to move every NFT within a specific collection owned by the user. Once the transaction is signed on the blockchain, the attacker uses their authorized contract to instantly transfer the victim’s high-value assets to a secondary wallet for liquidation on public marketplaces.
Chronology of Major Approval Exploits and Phishing Incidents
The evolution of approval-based theft can be traced through several high-profile incidents that have shaped the current security landscape of the Web3 industry.
- The OpenSea Phishing Incident (February 2022): In early 2022, a sophisticated phishing campaign targeted OpenSea users during a planned contract migration. Attackers sent spoofed emails appearing to be from OpenSea, directing users to sign a transaction to "migrate" their listings. Those who complied unknowingly signed an atomicMatch request—a legacy approval function—allowing the attacker to steal hundreds of NFTs, including Bored Ape Yacht Club and Mutant Ape Yacht Club assets, valued at approximately $1.7 million at the time.
- The BadgerDAO Hack (December 2021): This incident demonstrated that even legitimate platforms can be vectors for approval theft. Attackers compromised the front-end of the BadgerDAO website and injected a malicious script that prompted users to sign approvals for a rogue contract. This exploit resulted in the loss of over $120 million in assets, as users believed they were interacting with the protocol’s genuine smart contracts.
- The Multichain Fantom Bridge Exploit (July 2023): More recently, vulnerabilities in cross-chain bridges have highlighted the risks of "approval sprawl." When the Multichain bridge was compromised, security researchers urged users to immediately revoke all historical approvals associated with the bridge’s smart contracts. Even users who had not used the bridge for months remained at risk because their previous "infinite approvals" were still active on the blockchain.
The Vital Role of the Revoke Function
To counter the risks associated with persistent approvals, the "Revoke" function was developed. Revoking is the process of resetting an approval limit to zero, effectively "locking the door" that was previously opened. This does not affect the assets themselves; rather, it nullifies the permission previously granted to a specific smart contract.
Security experts recommend a "hygiene-first" approach to wallet management. This includes revoking permissions immediately after a trade is completed or at regular intervals (e.g., monthly). In cases where a platform is known to have been hacked or a user suspects they have interacted with a suspicious site, revoking permissions is the only way to stop an attacker from draining assets, even if the user has already disconnected their wallet from the site’s interface.
Revoke.cash: A Critical Tool for On-Chain Security
While users can manually revoke permissions through block explorers like Etherscan by interacting directly with contract code, the process is technical and prone to error. Tools like Revoke.cash have emerged as the industry standard for simplifying this process. These platforms aggregate all active approvals across multiple blockchain networks (including Ethereum, Polygon, Avalanche, and various Layer-2 solutions) and present them in a user-friendly dashboard.
Operational Guide for Revoke.cash:
- Connection and Chain Selection: Users connect their decentralized wallet (e.g., MetaMask or Rabby) to the platform. It is essential to select the correct network to see the permissions active on that specific chain.
- Filtering and Identification: The tool displays a list of all tokens and NFT collections for which permissions have been granted. It identifies the "Spender" (the contract with the permission) and the "Allowance" (the amount they can move).
- The Revocation Transaction: By clicking the "Revoke" button, the user triggers a new transaction. This transaction requires a small amount of gas (network fees) because it involves writing new data to the blockchain to update the permission status.
- Advanced Features: Modern iterations of Revoke.cash, such as those updated in 2025, include "Domain Scanners" and "Exploit Checkers." The Domain Scanner allows users to input a URL to check if it has been flagged as a phishing site before connecting their wallet. The Exploit Checker cross-references a user’s active approvals against a database of recently compromised smart contracts, providing an immediate alert if assets are at risk.
Supporting Data on Crypto Theft and Security Trends
The scale of the problem is reflected in industry data. According to Chainalysis, 2022 was the biggest year ever for crypto hacking, with $3.8 billion stolen from various protocols. A significant portion of these losses, particularly in the "individual wallet" category, was attributed to phishing and approval exploits.
Furthermore, a study of on-chain behavior suggests that the average DeFi user has over 15 active "infinite approvals" at any given time, many of which are for protocols the user no longer uses. This "approval debt" represents a massive, unaddressed attack surface. The move toward "Account Abstraction" (ERC-4337) is currently being hailed as a long-term solution. This technology allows for more granular control over permissions, such as setting expiration dates for approvals or requiring multi-signature authorization for large transfers, potentially rendering traditional approval phishing obsolete in future wallet generations.
Official Responses and Ecosystem Evolution
Regulatory bodies and major wallet providers have begun to respond to these threats. The FBI’s Internet Crime Complaint Center (IC3) has issued multiple alerts regarding "Web3 phishing," specifically highlighting the danger of signing unknown smart contract transactions.
In response, wallet providers like MetaMask and Rabby have updated their user interfaces to provide clearer warnings. Instead of a generic "Sign Transaction" prompt, modern wallets now attempt to decode the transaction, explicitly stating: "This transaction grants [Contract Name] permission to move all of your [Token Name]." These UI improvements are critical, as they provide the last line of defense against the psychological manipulation used by scammers.

Broader Implications and Best Practices for Asset Protection
The prevalence of approval exploits underscores a fundamental truth of the blockchain era: with total self-custody comes total responsibility. The "Approve" and "Revoke" functions are the gears of the decentralized economy, but without proper oversight, they can be turned against the user.
To maintain a secure digital asset portfolio, users should adhere to the following factual guidelines:

- Use a Hardware Wallet: Storing high-value NFTs and tokens on a hardware wallet (like Ledger or Trezor) adds a physical layer of security, making it harder for a simple "click" on a phishing site to result in a total loss.
- Bookmark Official Sites: Never use search engine results or social media links to access financial platforms. Always use verified bookmarks to ensure the URL is correct.
- The "Burner" Wallet Strategy: For minting new NFTs or interacting with unverified DeFi protocols, use a "burner" wallet with minimal funds. Only transfer assets to a "cold" storage wallet once the interaction is complete.
- Regular Audits: Use Revoke.cash or similar tools at least once a month to clear out unnecessary permissions.
In conclusion, while the blockchain offers unprecedented financial freedom, the technical nuances of smart contract interactions require constant vigilance. The "Approve" function is a necessary tool for utility, but the "Revoke" function is the essential tool for security. As the ecosystem matures and moves toward more secure standards like Account Abstraction, the most effective defense remains an informed and cautious user base. Understanding the chronology of past exploits and the mechanics of on-chain permissions is not merely an academic exercise; it is a fundamental requirement for anyone participating in the future of digital finance.